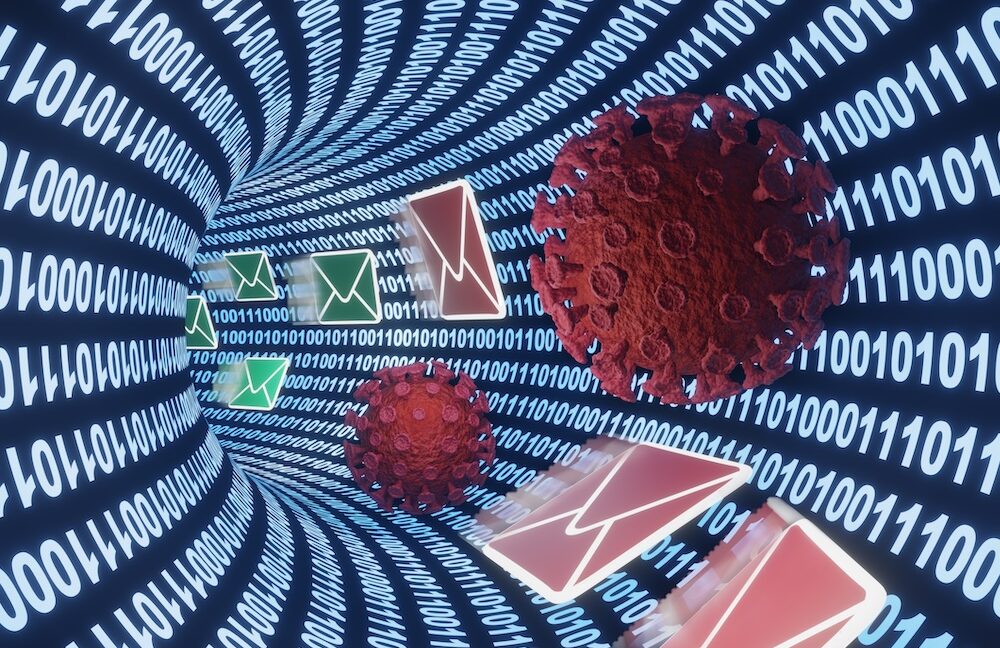
Two hacking groups, including a North Korea–linked unit, have begun using EtherHiding to distribute malware by embedding payloads inside smart contracts on public blockchains such as Ethereum and the BNB Smart Chain. Google Threat Intelligence Group researchers say this technique creates a portable, resilient form of “bulletproof” hosting that is difficult for authorities to remove.
EtherHiding relies on smart contracts that automatically enforce terms when specified conditions are met. Because these contracts live on decentralized networks, there is no central portal to delete the code or takedown the payload, complicating attempts at takedowns by law enforcement and security researchers alike.
The approach offers several advantages over traditional malware delivery methods. It can reduce hosting costs while spreading components across multiple blockchains, enabling operators to update payloads by modifying contract logic and making transaction histories harder to trace back to individuals.
Researchers say UNC5342, a North Korea–backed group, has used JadeSnow to stage infections and retrieve later-stage payloads from both Ethereum and the BNB chain. A second group, UNC5142, has also been observed employing EtherHiding, highlighting how actors are adapting blockchain technology to sustain operations and complicate attribution.
Analysts note this development underscores North Korea’s growing cyber capabilities. Elliptic recently reported that the regime has stolen cryptocurrency valued at more than $2 billion in 2025, illustrating the scale at which adversaries may leverage blockchain ecosystems for illicit gain, including malware distribution and related activities.














![[AS52888] Universidade Federal de São Carlos (4 probes)](https://r2.isp.tools/images/asn/52888/logo/image_100px.png)
![[AS262393] TIG.com VOCÊ!](https://r2.isp.tools/images/asn/262393/logo/image_100px.png)
